- Sort dependencies and features sections.
- Add `tidy` markers to the sorted sections so they stay sorted.
- Remove empty `[lib`] sections.
- Remove "See more keys..." comments.
Excluded files:
- rustc_codegen_{cranelift,gcc}, because they're external.
- rustc_lexer, because it has external use.
- stable_mir, because it has external use.
Consider alias bounds when computing liveness in NLL (but this time sound hopefully)
This is a revival of #116040, except removing the changes to opaque lifetime captures check to make sure that we're not triggering any unsoundness due to the lack of general existential regions and the currently-existing `ReErased` hack we use instead.
r? `@aliemjay` -- I appreciate you pointing out the unsoundenss in the previous iteration of this PR, and I'd like to hear that you're happy with this iteration of this PR before this goes back into FCP :>
Fixes#116794 as well
---
(mostly copied from #116040 and reworked slightly)
# Background
Right now, liveness analysis in NLL is a bit simplistic. It simply walks through all of the regions of a type and marks them as being live at points. This is problematic in the case of aliases, since it requires that we mark **all** of the regions in their args[^1] as live, leading to bugs like #42940.
In reality, we may be able to deduce that fewer regions are allowed to be present in the projected type (or "hidden type" for opaques) via item bounds or where clauses, and therefore ideally, we should be able to soundly require fewer regions to be live in the alias.
For example:
```rust
trait Captures<'a> {}
impl<T> Captures<'_> for T {}
fn capture<'o>(_: &'o mut ()) -> impl Sized + Captures<'o> + 'static {}
fn test_two_mut(mut x: ()) {
let _f1 = capture(&mut x);
let _f2 = capture(&mut x);
//~^ ERROR cannot borrow `x` as mutable more than once at a time
}
```
In the example above, we should be able to deduce from the `'static` bound on `capture`'s opaque that even though `'o` is a captured region, it *can never* show up in the opaque's hidden type, and can soundly be ignored for liveness purposes.
# The Fix
We apply a simple version of RFC 1214's `OutlivesProjectionEnv` and `OutlivesProjectionTraitDef` rules to NLL's `make_all_regions_live` computation.
Specifically, when we encounter an alias type, we:
1. Look for a unique outlives bound in the param-env or item bounds for that alias. If there is more than one unique region, bail, unless any of the outlives bound's regions is `'static`, and in that case, prefer `'static`. If we find such a unique region, we can mark that outlives region as live and skip walking through the args of the opaque.
2. Otherwise, walk through the alias's args recursively, as we do today.
## Limitation: Multiple choices
This approach has some limitations. Firstly, since liveness doesn't use the same type-test logic as outlives bounds do, we can't really try several options when we're faced with a choice.
If we encounter two unique outlives regions in the param-env or bounds, we simply fall back to walking the opaque via its args. I expect this to be mostly mitigated by the special treatment of `'static`, and can be fixed in a forwards-compatible by a more sophisticated analysis in the future.
## Limitation: Opaque hidden types
Secondly, we do not employ any of these rules when considering whether the regions captured by a hidden type are valid. That causes this code (cc #42940) to fail:
```rust
trait Captures<'a> {}
impl<T> Captures<'_> for T {}
fn a() -> impl Sized + 'static {
b(&vec![])
}
fn b<'o>(_: &'o Vec<i32>) -> impl Sized + Captures<'o> + 'static {}
```
We need to have existential regions to avoid [unsoundness](https://github.com/rust-lang/rust/pull/116040#issuecomment-1751628189) when an opaque captures a region which is not represented in its own substs but which outlives a region that does.
## Read more
Context: https://github.com/rust-lang/rust/pull/115822#issuecomment-1731153952 (for the liveness case)
More context: https://github.com/rust-lang/rust/issues/42940#issuecomment-455198309 (for the opaque capture case, which this does not fix)
[^1]: except for bivariant region args in opaques, which will become less relevant when we move onto edition 2024 capture semantics for opaques.
See through aggregates in GVN
This PR is extracted from https://github.com/rust-lang/rust/pull/111344
The first 2 commit are cleanups to avoid repeated work. I propose to stop removing useless assignments as part of this pass, and let a later `SimplifyLocals` do it. This makes tests easier to read (among others).
The next 3 commits add a constant folding mechanism to the GVN pass, presented in https://github.com/rust-lang/rust/pull/116012. ~This pass is designed to only use global allocations, to avoid any risk of accidental modification of the stored state.~
The following commits implement opportunistic simplifications, in particular:
- projections of aggregates: `MyStruct { x: a }.x` gets replaced by `a`, works with enums too;
- projections of arrays: `[a, b][0]` becomes `a`;
- projections of repeat expressions: `[a; N][x]` becomes `a`;
- transform arrays of equal operands into a repeat rvalue.
Fixes https://github.com/rust-lang/miri/issues/3090
r? `@oli-obk`
Rollup of 5 pull requests
Successful merges:
- #115968 (Don't use LFS64 symbols on musl)
- #117043 (add bootstrap flag `--skip-stage0-validation`)
- #117082 (Fix closure-inherit-target-feature test for SGX platform)
- #117312 (memcpy assumptions: link to source showing that GCC makes the same assumption)
- #117337 (rustdoc: Use `ThinVec` in `GenericParamDefKind`)
r? `@ghost`
`@rustbot` modify labels: rollup
rustdoc: Use `ThinVec` in `GenericParamDefKind`
This should hopefully reduce memory usage and improve performance since
these vectors are often empty (and `GenericParamDefKind` is constructed *a lot*).
memcpy assumptions: link to source showing that GCC makes the same assumption
I finally stumbled upon a source showing that GCC also generates overlapping `memcpy`. So if we're linking major C compilers making such assumptions here, let's have both clang and GCC.
Fix closure-inherit-target-feature test for SGX platform
PR #116078 adds the `closure-inherit-target-feature.rs` test that checks the generated assembly code for closures. These checks explicitly check the presence of `ret` instructions. This is incompatible with the SGX target as it explicitly rewrites all `ret` instructions to mitigate LVI vulnerabilities of certain processors. This PR simply ignores these tests for the SGX platform.
cc: ```@jethrogb```
add bootstrap flag `--skip-stage0-validation`
This change introduces the `--skip-stage0-validation` flag, which permits the use of any desired version of the stage0 compiler without verifying its version.
Additionally, stage0 compiler validation check is reverted(#115103) to its default enabled state.
Helps to #115065
r? Mark-Simulacrum
Don't use LFS64 symbols on musl
Supersedes #106246
~~Note to packagers: If your distro's musl package has already been updated, then you won't be able to build a newer version of rust until a new rust release is made with these changes merged (which can be used to bootstrap). I'm using a super hacky method to bypass this by creating a stub library with LFS64 symbols and building a patched rust, so the symbols satisfy the build requirements while the final compiler build has no references to LFS64 symbols, example: https://codeberg.org/kiss-community/repo/pulls/160/files~~ Doesn't seem to be necessary with new rustup nightly builds, likely due to updates to vendored crates
cc ```@alyssais```
This should hopefully reduce memory usage and improve performance since
these vectors are often empty (and `GenericParamDefKind` is constructed
*a lot*).
Rollup of 5 pull requests
Successful merges:
- #115773 (tvOS simulator support on Apple Silicon for rustc)
- #117162 (Remove `cfg_match` from the prelude)
- #117311 (-Zunpretty help: add missing possible values)
- #117316 (Mark constructor of `BinaryHeap` as const fn)
- #117319 (explain why we don't inline when target features differ)
r? `@ghost`
`@rustbot` modify labels: rollup
change default output mode of `BootstrapCommand`
`SuppressOnSuccess` on `BootstrapCommand` is a problematic default mode as it affects the logs during the bootstrapping (as shown in the screenshot below). The default behavior should be to print everything unless we explicitly modify the behavior within build steps.
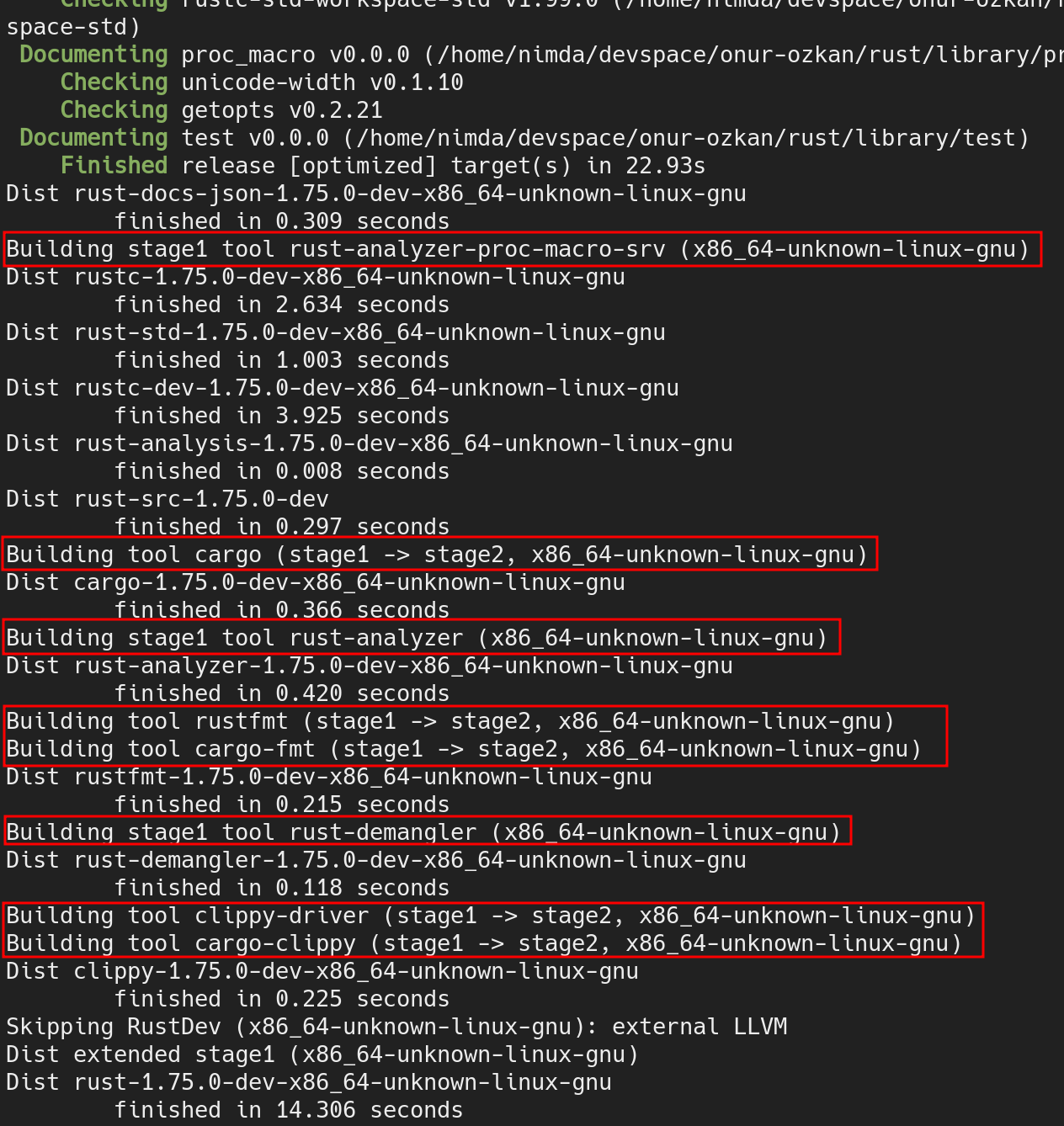
Fixes#117315
cc `@Kobzol`
Declare rustc_target's dependency on object/macho
Without this, `cargo check` fails in crates that depend on rustc_target.
<details>
<summary>`cargo check` diagnostics</summary>
```console
Checking rustc_target v0.0.0
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:176:17
|
176 | object::macho::PLATFORM_MACOS => Some((13, 1)),
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:177:17
|
177 | object::macho::PLATFORM_IOS
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:178:19
|
178 | | object::macho::PLATFORM_IOSSIMULATOR
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:179:19
|
179 | | object::macho::PLATFORM_TVOS
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:180:19
|
180 | | object::macho::PLATFORM_TVOSSIMULATOR
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:181:19
|
181 | | object::macho::PLATFORM_MACCATALYST => Some((16, 2)),
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:182:17
|
182 | object::macho::PLATFORM_WATCHOS | object::macho::PLATFORM_WATCHOSSIMULATOR => Some((9, 1)),
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:182:51
|
182 | object::macho::PLATFORM_WATCHOS | object::macho::PLATFORM_WATCHOSSIMULATOR => Some((9, 1)),
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:189:33
|
189 | ("macos", _) => object::macho::PLATFORM_MACOS,
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:190:38
|
190 | ("ios", "macabi") => object::macho::PLATFORM_MACCATALYST,
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:191:35
|
191 | ("ios", "sim") => object::macho::PLATFORM_IOSSIMULATOR,
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:192:31
|
192 | ("ios", _) => object::macho::PLATFORM_IOS,
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:193:39
|
193 | ("watchos", "sim") => object::macho::PLATFORM_WATCHOSSIMULATOR,
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:194:35
|
194 | ("watchos", _) => object::macho::PLATFORM_WATCHOS,
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:195:36
|
195 | ("tvos", "sim") => object::macho::PLATFORM_TVOSSIMULATOR,
| ^^^^^ could not find `macho` in `object`
error[E0433]: failed to resolve: could not find `macho` in `object`
--> compiler/rustc_target/src/spec/apple_base.rs:196:32
|
196 | ("tvos", _) => object::macho::PLATFORM_TVOS,
| ^^^^^ could not find `macho` in `object`
```
</details>
`rustc_target` unconditionally contains its `spec` module (i.e. there is no `#[cfg]` on the `mod spec;`). The `spec/mod.rs` also does not start with `#![cfg]`.
aa91057796/compiler/rustc_target/src/lib.rs (L37)
Similarly, the `spec` module unconditionally contains `apple_base`.
aa91057796/compiler/rustc_target/src/spec/mod.rs (L62)
And, `apple_base` unconditionally refers to `object::macho`.
aa91057796/compiler/rustc_target/src/spec/apple_base.rs (L176)
So I figure there is no way `object::macho` isn't needed by rustc.
`object::macho` only exists if the `object` crate's "macho" feature is enabled. https://github.com/gimli-rs/object/blob/0.32.0/src/lib.rs#L111-L112
Add support for i586-unknown-netbsd as target.
This restricts instructions to those offered by Pentium, to support e.g. AMD Geode.
There is already an entry for this target in the NetBSD platform support page at
src/doc/rustc/src/platform-support/netbsd.md
...so this should forestall its removal.
Additional fixes are needed for some vendored modules, this is the changes in the rust compiler core itself.
tvOS simulator support on Apple Silicon for rustc
Closes or is a subtask of #115692.
# Tier 3 Target Policy
At this tier, the Rust project provides no official support for a target, so we place minimal requirements on the introduction of targets.
> * A tier 3 target must have a designated developer or developers (the "target maintainers") on record to be CCed when issues arise regarding the target. (The mechanism to track and CC such developers may evolve over time.)
See [`src/doc/rustc/src/platform-support/apple-tvos.md`](4ab4d48ee5/src/doc/rustc/src/platform-support/apple-tvos.md)
> * Targets must use naming consistent with any existing targets; for instance, a target for the same CPU or OS as an existing Rust target should use the same name for that CPU or OS. Targets should normally use the same names and naming conventions as used elsewhere in the broader ecosystem beyond Rust (such as in other toolchains), unless they have a very good reason to diverge. Changing the name of a target can be highly disruptive, especially once the target reaches a higher tier, so getting the name right is important even for a tier 3 target.
> * Target names should not introduce undue confusion or ambiguity unless absolutely necessary to maintain ecosystem compatibility. For example, if the name of the target makes people extremely likely to form incorrect beliefs about what it targets, the name should be changed or augmented to disambiguate it.
> * If possible, use only letters, numbers, dashes and underscores for the name. Periods (.) are known to cause issues in Cargo.
This naming scheme matches `$ARCH-$VENDOR-$OS-$ABI` (I think `sim` is the ABI here) which is matches the iOS apple silicon simulator (`aarch64-apple-ios-sim`). [There is some discussion about renaming some apple simulator targets](https://github.com/rust-lang/rust/issues/115692#issuecomment-1712931910) to match the `-sim` suffix but that is outside the scope of this PR.
> * Tier 3 targets may have unusual requirements to build or use, but must not create legal issues or impose onerous legal terms for the Rust project or for Rust developers or users.
>
> * The target must not introduce license incompatibilities.
> * Anything added to the Rust repository must be under the standard Rust license (MIT OR Apache-2.0).
> * The target must not cause the Rust tools or libraries built for any other host (even when supporting cross-compilation to the target) to depend on any new dependency less permissive than the Rust licensing policy. This applies whether the dependency is a Rust crate that would require adding new license exceptions (as specified by the tidy tool in the rust-lang/rust repository), or whether the dependency is a native library or binary. In other words, the introduction of the target must not cause a user installing or running a version of Rust or the Rust tools to be subject to any new license requirements.
> * Compiling, linking, and emitting functional binaries, libraries, or other code for the target (whether hosted on the target itself or cross-compiling from another target) must not depend on proprietary (non-FOSS) libraries. Host tools built for the target itself may depend on the ordinary runtime libraries supplied by the platform and commonly used by other applications built for the target, but those libraries must not be required for code generation for the target; cross-compilation to the target must not require such libraries at all. For instance, rustc built for the target may depend on a common proprietary C runtime library or console output library, but must not depend on a proprietary code generation library or code optimization library. Rust's license permits such combinations, but the Rust project has no interest in maintaining such combinations within the scope of Rust itself, even at tier 3.
> * "onerous" here is an intentionally subjective term. At a minimum, "onerous" legal/licensing terms include but are not limited to: non-disclosure requirements, non-compete requirements, contributor license agreements (CLAs) or equivalent, "non-commercial"/"research-only"/etc terms, requirements conditional on the employer or employment of any particular Rust developers, revocable terms, any requirements that create liability for the Rust project or its developers or users, or any requirements that adversely affect the livelihood or prospects of the Rust project or its developers or users.
This contribution is fully available under the standard Rust license with no additional legal restrictions whatsoever. This PR does not introduce any new dependency less permissive than the Rust license policy.
The new targets do not depend on proprietary libraries.
> * Tier 3 targets should attempt to implement as much of the standard libraries as possible and appropriate (core for most targets, alloc for targets that can support dynamic memory allocation, std for targets with an operating system or equivalent layer of system-provided functionality), but may leave some code unimplemented (either unavailable or stubbed out as appropriate), whether because the target makes it impossible to implement or challenging to implement. The authors of pull requests are not obligated to avoid calling any portions of the standard library on the basis of a tier 3 target not implementing those portions.
This new target implements as much of the standard library as the other tvOS targets do.
> * The target must provide documentation for the Rust community explaining how to build for the target, using cross-compilation if possible. If the target supports running binaries, or running tests (even if they do not pass), the documentation must explain how to run such binaries or tests for the target, using emulation if possible or dedicated hardware if necessary.
I have added the target to the other tvOS targets in [`src/doc/rustc/src/platform-support/apple-tvos.md`](4ab4d48ee5/src/doc/rustc/src/platform-support/apple-tvos.md)
> * Neither this policy nor any decisions made regarding targets shall create any binding agreement or estoppel by any party. If any member of an approving Rust team serves as one of the maintainers of a target, or has any legal or employment requirement (explicit or implicit) that might affect their decisions regarding a target, they must recuse themselves from any approval decisions regarding the target's tier status, though they may otherwise participate in discussions.
> * This requirement does not prevent part or all of this policy from being cited in an explicit contract or work agreement (e.g. to implement or maintain support for a target). This requirement exists to ensure that a developer or team responsible for reviewing and approving a target does not face any legal threats or obligations that would prevent them from freely exercising their judgment in such approval, even if such judgment involves subjective matters or goes beyond the letter of these requirements.
> * Tier 3 targets must not impose burden on the authors of pull requests, or other developers in the community, to maintain the target. In particular, do not post comments (automated or manual) on a PR that derail or suggest a block on the PR based on a tier 3 target. Do not send automated messages or notifications (via any medium, including via ``@)`` to a PR author or others involved with a PR regarding a tier 3 target, unless they have opted into such messages.
> * Backlinks such as those generated by the issue/PR tracker when linking to an issue or PR are not considered a violation of this policy, within reason. However, such messages (even on a separate repository) must not generate notifications to anyone involved with a PR who has not requested such notifications.
> * Patches adding or updating tier 3 targets must not break any existing tier 2 or tier 1 target, and must not knowingly break another tier 3 target without approval of either the compiler team or the maintainers of the other tier 3 target.
> * In particular, this may come up when working on closely related targets, such as variations of the same architecture with different features. Avoid introducing unconditional uses of features that another variation of the target may not have; use conditional compilation or runtime detection, as appropriate, to let each target run code supported by that target.
I acknowledge these requirements and intend to ensure that they are met.
This target does not touch any existing tier 2 or tier 1 targets and should not break any other targets.
Implement `gen` blocks in the 2024 edition
Coroutines tracking issue https://github.com/rust-lang/rust/issues/43122
`gen` block tracking issue https://github.com/rust-lang/rust/issues/117078
This PR implements `gen` blocks that implement `Iterator`. Most of the logic with `async` blocks is shared, and thus I renamed various types that were referring to `async` specifically.
An example usage of `gen` blocks is
```rust
fn foo() -> impl Iterator<Item = i32> {
gen {
yield 42;
for i in 5..18 {
if i.is_even() { continue }
yield i * 2;
}
}
}
```
The limitations (to be resolved) of the implementation are listed in the tracking issue
coverage: Consistently remove unused counter IDs from expressions/mappings
If some coverage counters were removed by MIR optimizations, we need to take care not to refer to those counter IDs in coverage mappings, and instead replace them with a constant zero value. If we don't, `llvm-cov` might see a too-large counter ID and silently discard the entire function from its coverage reports.
Fixes#117012.
Distribute cg_clif as rustup component on the nightly channel
This makes it possible to use cg_clif using:
```bash
$ rustup component add rustc-codegen-cranelift-preview --toolchain nightly
$ RUSTFLAGS="-Zcodegen-backend=cranelift" cargo +nightly build
```
cc https://github.com/rust-lang/compiler-team/issues/405.
r? `@Mark-Simulacrum`
This triggers a consistency check in rust (that all linker flavours
must have identical arguments), and on NetBSD/i386, the 32-bitness
is implicitly chosen through the chosen toolchain, and appears to
not be required. So drop it, and also drop the imports of the
now-no-longer-used identifiers.
Bump stdarch submodule and remove special handling for LLVM intrinsics that are no longer needed
Bumps stdarch to pull https://github.com/rust-lang/stdarch/pull/1477, which reimplemented some functions with portable SIMD intrinsics instead of arch specific LLVM intrinsics.
Handling of those LLVM intrinsics is removed from cranelift codegen and miri.
cc `@RalfJung` `@bjorn3`
Cleanup and improve `--check-cfg` implementation
This PR removes some indentation in the code, as well as preventing some bugs/misusages and fix a nit in the doc.
r? ```@petrochenkov``` (maybe)
When encountering sealed traits, point types that implement it
```
error[E0277]: the trait bound `S: d::Hidden` is not satisfied
--> $DIR/sealed-trait-local.rs:53:20
|
LL | impl c::Sealed for S {}
| ^ the trait `d::Hidden` is not implemented for `S`
|
note: required by a bound in `c::Sealed`
--> $DIR/sealed-trait-local.rs:17:23
|
LL | pub trait Sealed: self::d::Hidden {
| ^^^^^^^^^^^^^^^ required by this bound in `Sealed`
= note: `Sealed` is a "sealed trait", because to implement it you also need to implement `c::d::Hidden`, which is not accessible; this is usually done to force you to use one of the provided types that already implement it
= help: the following types implement the trait:
- c::X
- c::Y
```
The last `help` is new.
Create `windows/api.rs` for safer FFI
FFI is inherently unsafe. For memory safety we need to assert that some contract is being upheld on both sides of the FFI, though of course we can only ever check our side. In Rust, `unsafe` blocks are used to assert safety and `// SAFETY` comments describing why it is safe. Currently in sys/windows we have a lot of this unsafety spread all over the place, with variations on the same unsafe patterns repeated. And because of the repitition and frequency, we're a bit lax with the safety comments.
This PR aims to fix this and to make FFI safety more auditable by creating an `api` module with the goal of centralising and consolidating this unsafety. It contains thin wrappers around the Windows API that make most functions safe to call or, if that's not possible, then at least safer. Note that its goal is *only* to address safety. It does not stray far from the Windows API and intentionally does not attempt to make higher lever wrappers around, for example, file handles. This is better left to the existing modules. The windows/api.rs file has a top level comment to help future contributors understand the intent of the module and the design decisions made.
I chose two functions as a first tentative step towards the above goal:
- [`GetLastError`](https://learn.microsoft.com/en-us/windows/win32/api/errhandlingapi/nf-errhandlingapi-getlasterror) is trivially safe. There's no reason to wrap it in an `unsafe` block every time. So I simply created a safe `get_last_error` wrapper.
- [`SetFileInformationByHandle`](https://learn.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-setfileinformationbyhandle) is more complex. It essentially takes a generic type but over a C API which necessitates some amount of ceremony. Rather than implementing similar unsafe patterns in multiple places, I provide a safe `set_file_information_by_handle` that takes a Rusty generic type and handles converting that to the form required by the C FFI.
r? libs